How to setup SAML SSO for your Google Workspace
Last updated: March 17, 2026
Configure single sign-on to let your team access Fireflies securely through your Google Workspace identity provider.
🚀 Before You Begin
Setting up SSO involves configuring both your identity provider (Google Workspace) and Fireflies. Here's what you need to know before starting.
💡What You'll Need
Super Admin access to your Google Workspace Admin Console (admin.google.com)
Admin access to your Fireflies account
About 10–15 minutes to complete the full setup process
Two browser tabs — one for Google Admin Console, one for Fireflies
📌 Important Setup Requirement
Before you start the SSO configuration process, you must either:
Log out of your current Fireflies session, OR
Open the SSO setup link in an incognito/private browser window
This prevents session conflicts that can cause setup issues.
✅ How the Process Works
The setup follows three phases:
First, you'll create a custom SAML application in Google Admin Console and collect the IdP details.
Second, you'll configure Fireflies at
app.fireflies.ai/auth/ssousing those details.Third, you'll return to Google to finalize the connection with the callback URL fro Fireflies.
Part 1: Create a Custom SAML App in Google Workspace
1. Sign in to the Google Admin Console
Go to admin.google.com and sign in with your Super Admin account.
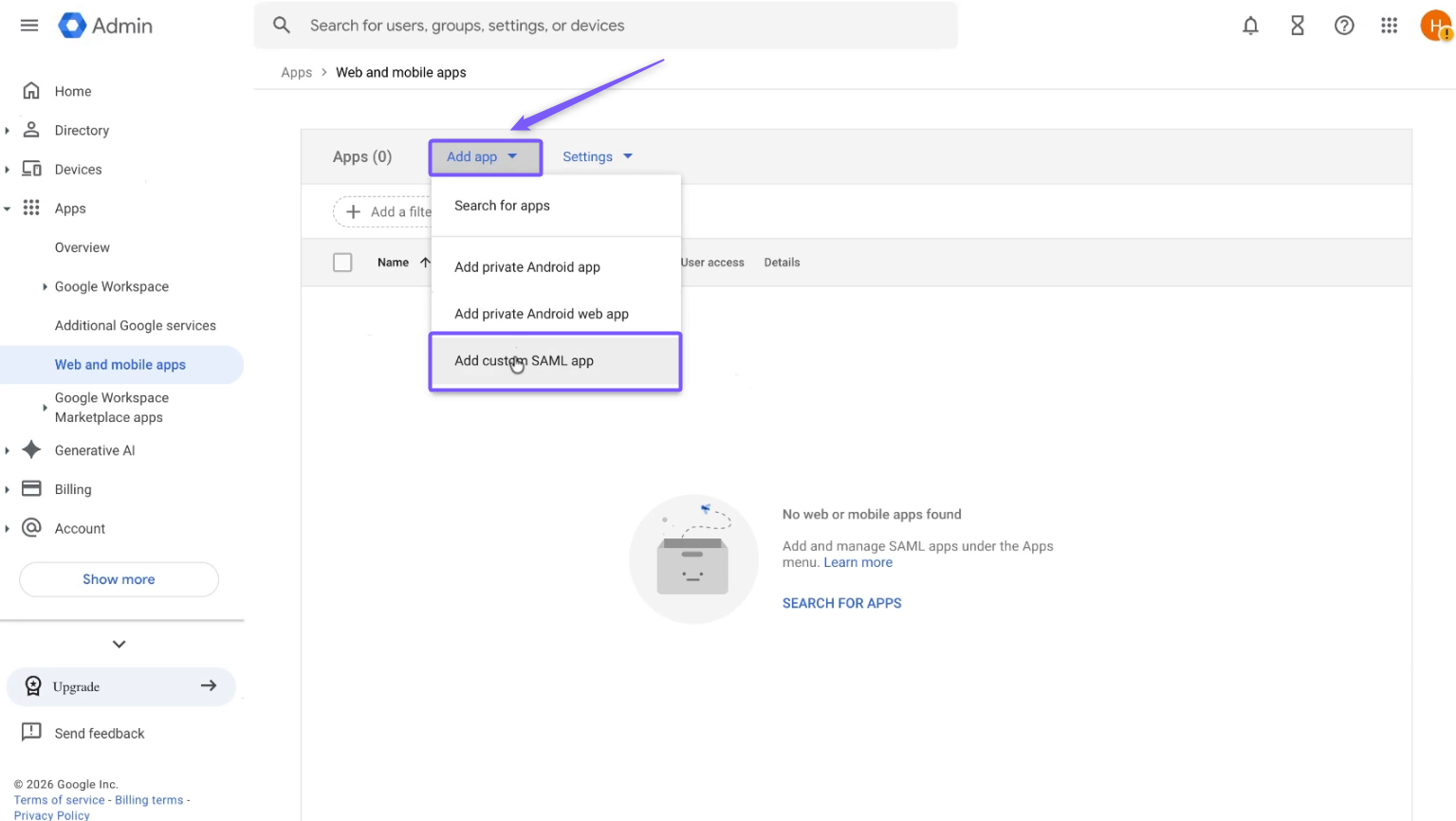
2. Navigate to Web and mobile apps
From the Admin Console home page, go to Menu → Apps → Web and mobile apps.
3. Add a custom SAML app
Click Add app → Add custom SAML app.
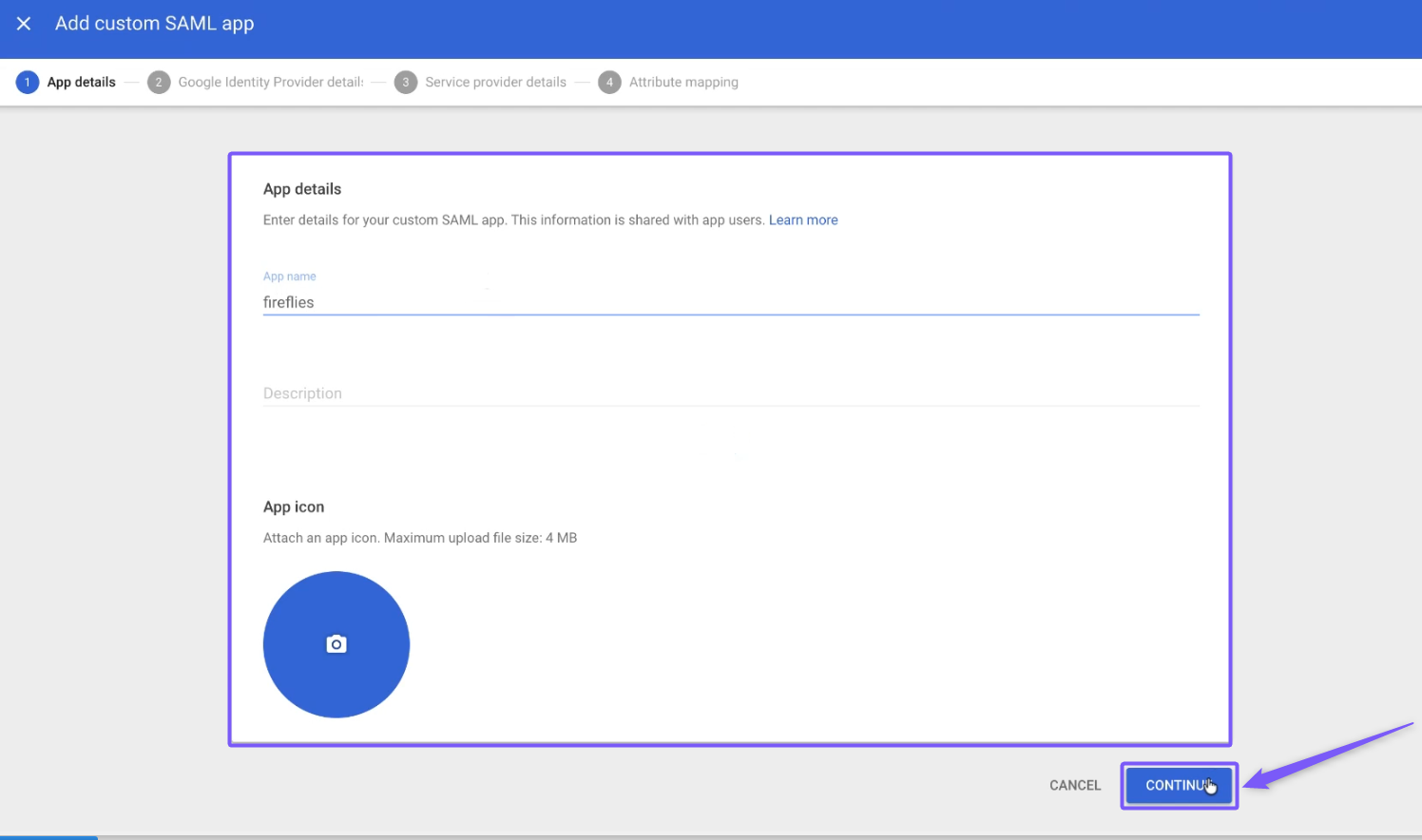
4. Enter the app details
In the App name field, enter "Fireflies" (or a descriptive name like "Fireflies SSO").
Optionally upload an icon for the app.
Click Continue.
5. Copy the Google Identity Provider details
On the Google Identity Provider details page, you will see the SSO URL, Entity ID, and Certificate. You need to collect these for the Fireflies configuration:
Copy the SSO URL (you'll paste this into Fireflies as the IDP Sign-in URL)
Download the Certificate (you'll upload this .pem file to Fireflies)
Click Continue.

Keep this tab open — you’ll need to come back to it after configuring Fireflies.
You can also download the IdP metadata file as an alternative.
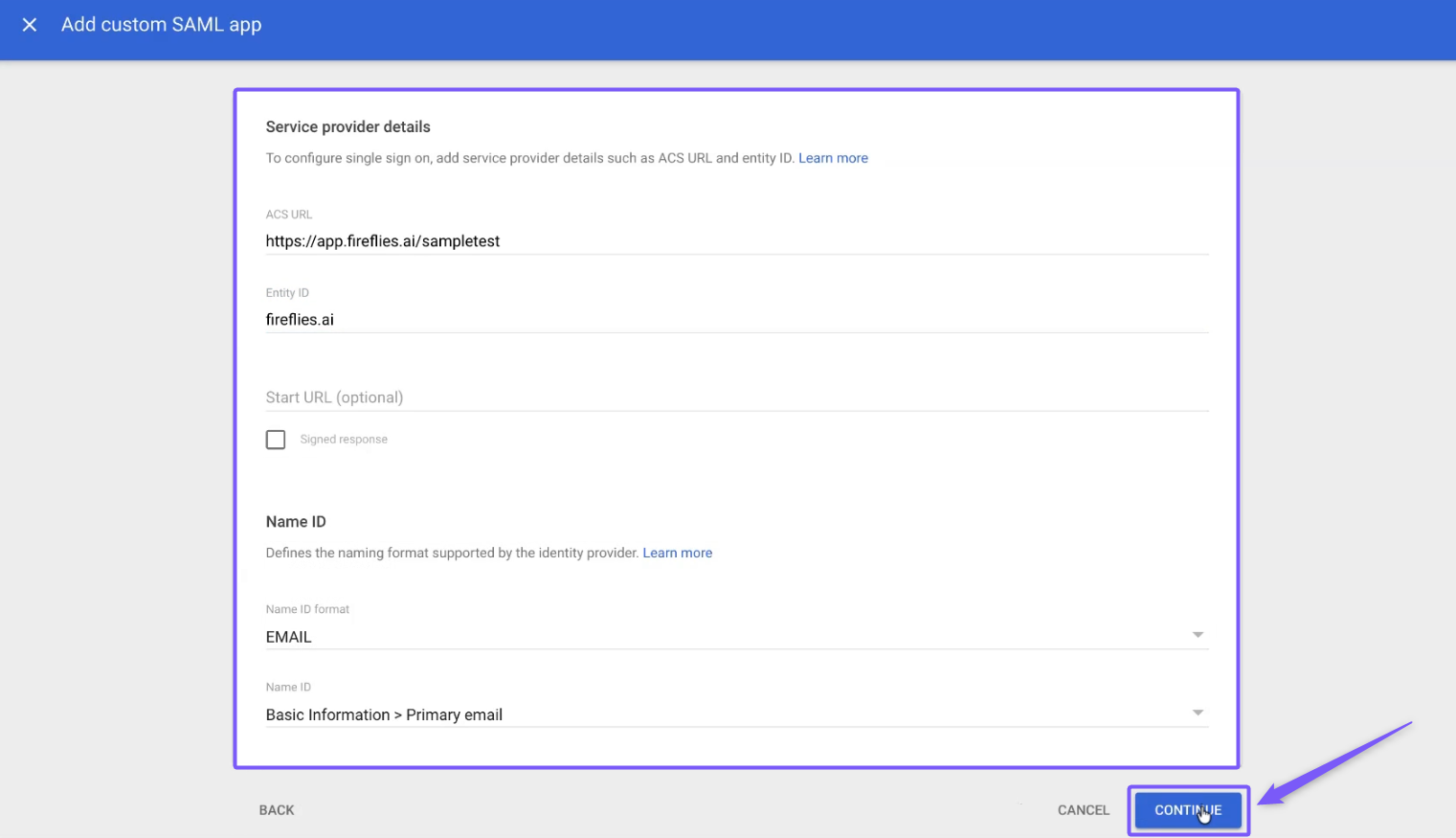
6. Enter Service Provider details
On the Service Provider Details page, enter the following information:
Field | Value |
ACS URL |
|
Entity ID |
|
Start URL | (Leave blank for now) |
Signed Response | Leave unchecked (default) |
Name ID Format | |
Name ID | Basic Information > Primary email |
Click Continue.
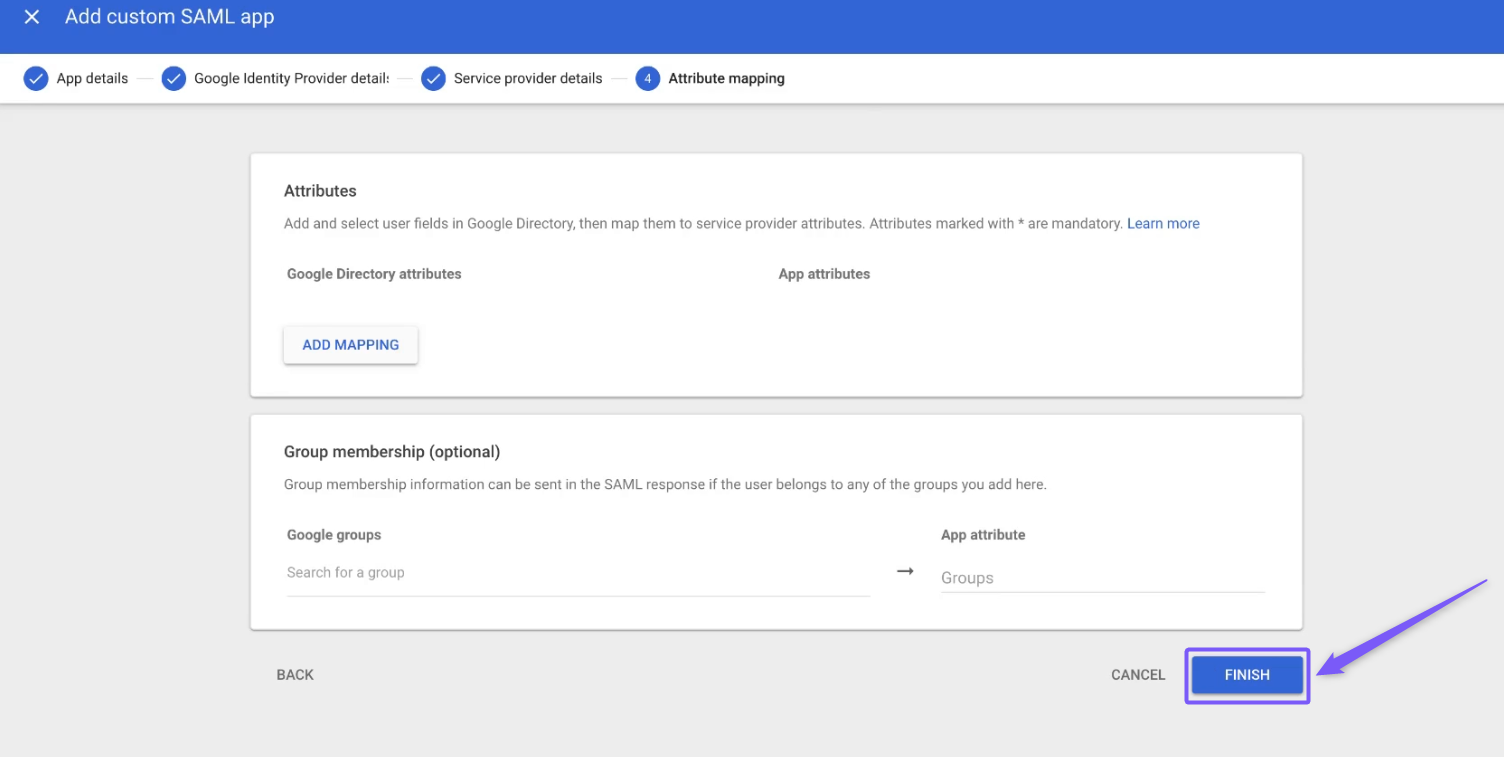
7. Configure Attribute Mapping (optional)
Attribute mapping is optional for basic Fireflies SSO. You can skip this step or add mappings if needed by your organization.
Click Finish.
Part 2: Verify Your Domain and Configure SSO in Fireflies
8. Initiate the SSO setup in Fireflies
Open a new browser tab and go to: https://app.fireflies.ai/auth/sso
Enter your admin email address and submit.
Fireflies will send you an email with detailed setup instructions and a unique configuration link.
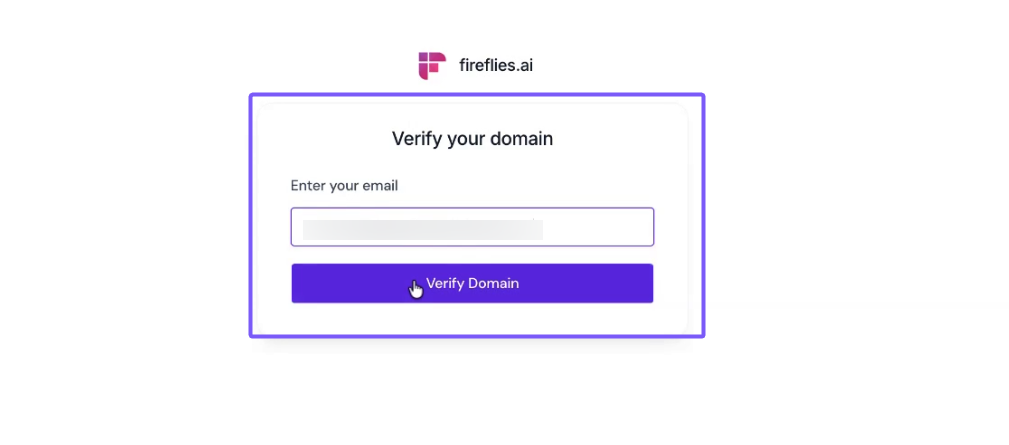
⚠ Important: Domain Verification Required
You must complete domain verification before proceeding. The SSO configuration link will only become available after your domain is verified.
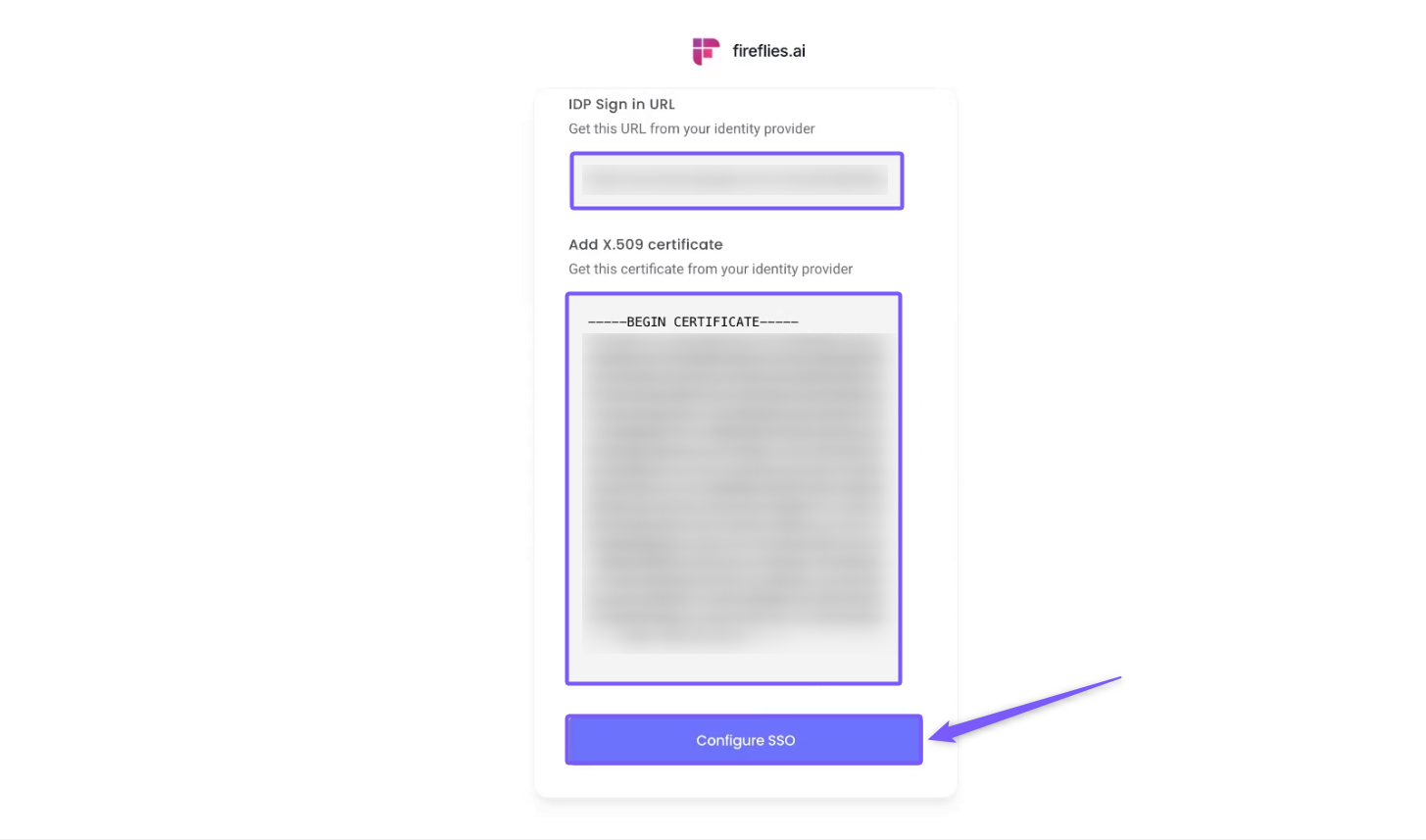
10. Configure SSO in Fireflies
Once your domain is verified, click the unique SSO configuration link provided in the setup email from Fireflies.
The SSO configuration link is only accessible through the setup email and cannot be accessed directly. Ensure you are logged out of Fireflies or using an incognito window before clicking the link.
On the SSO configuration page, enter the following details:
Paste the SSO URL from Google (Step 5) into the IDP Sign-in URL field.
Upload the .pem certificate file downloaded from Google (Step 5) to the Add X.509 Certificate field.
Click Configure SSO to complete the setup.
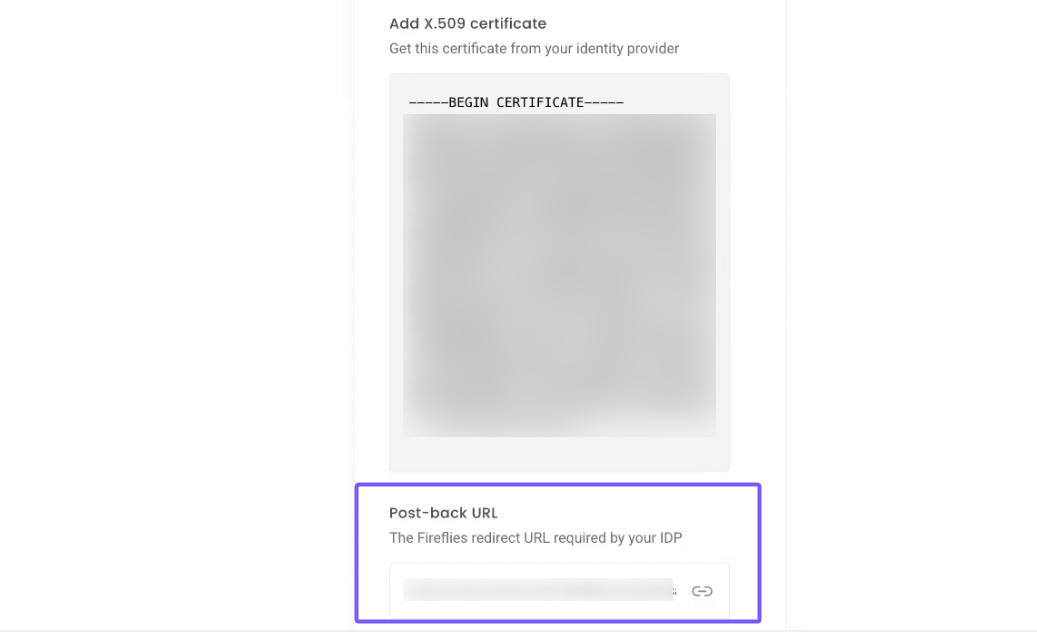
11. Copy the Post-back URL from Fireflies
After clicking Configure SSO, Fireflies will provide:
• A Post-back URL (ACS Consumer URL) — needed to update Google’s ACS URL
• A unique Login URL for your users
Save both URLs. The Post-back URL is needed for the next step, and the Login URL is what your team will use for SSO sign-in.
Part 3: Complete the Google Configuration
12. Update the ACS URL in Google Admin Console
Return to your Google Admin Console tab.
Go to: Apps → Web and mobile apps → Fireflies
Click Service Provider Details.
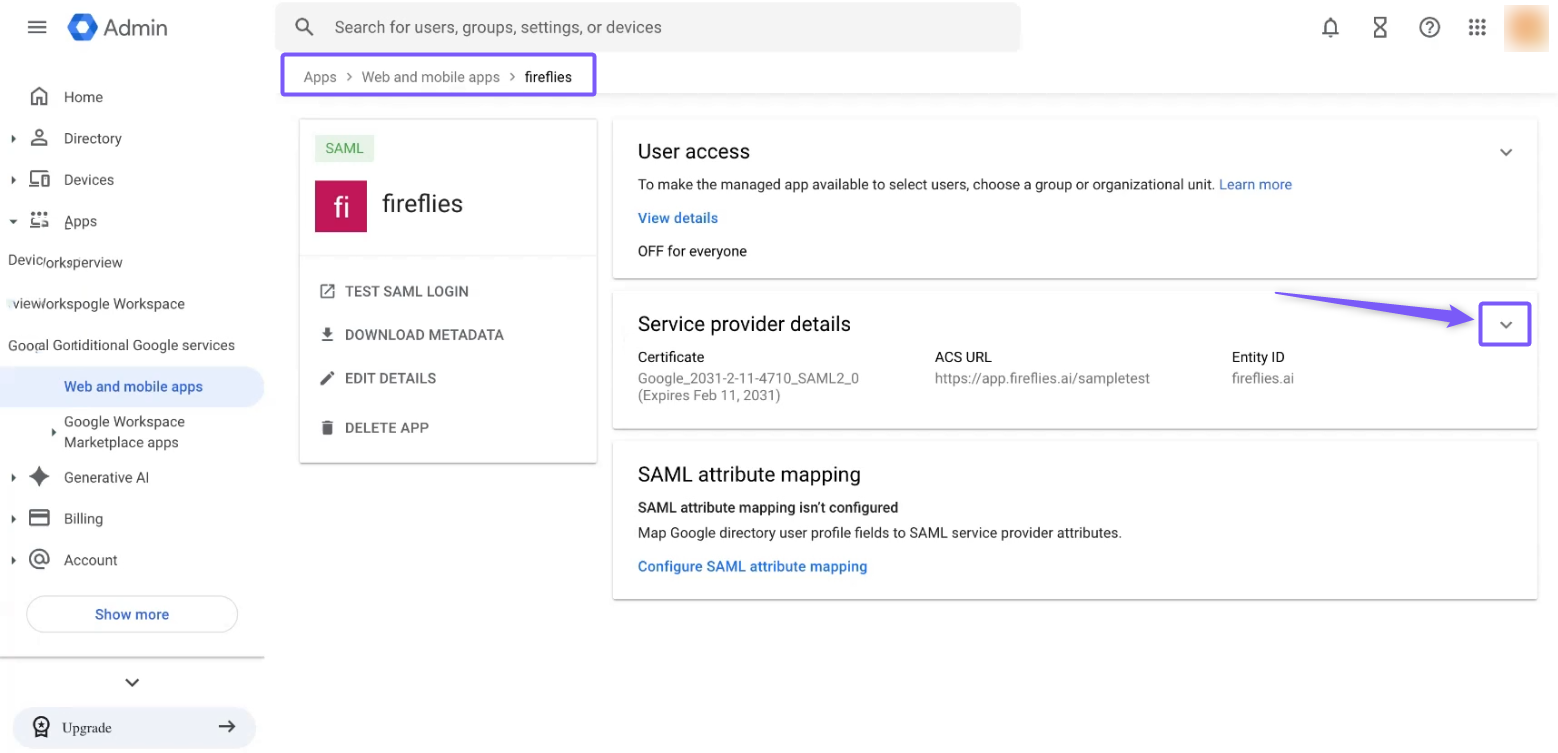
Replace the temporary ACS URL
https://app.fireflies.ai/sampletestwith the Post-back URL from Fireflies.
Field | Value |
ACS URL | Post-back URL from Fireflies |
Entity ID |
|
Click Save.
13. Turn on user access
In the Fireflies app settings in Google Admin Console:
Click User access
Set the Service status to ON for everyone (or select specific organizational units)
Click Save.
Users must be assigned to the app (either through "ON for everyone" or by
selecting specific organizational units) before they can sign in via SSO
14. Test the SSO connection
In Google Admin Console, click Test SAML login at the top of the Fireflies app page. You should be redirected to Google sign-in and then back to Fireflies after authentication.
📌Enforced SSO Redirect Behavior
When SSO is enforced on your domain:
Users will be automatically redirected to your organization's SSO login link when they attempt to log in via Google or Microsoft OAuth.
This happens after the OAuth authentication succeeds—at which point Fireflies checks if your domain has an enforced SSO configuration and triggers the redirect.
Avoid this behavior
If your users don't want automatic redirects, have them use your unique SSO login link instead of the generic Google or Microsoft login options.
❓Troubleshooting
1. Why am I seeing a “session conflict” error?
Make sure you logged out of Fireflies or are using an incognito/private browser window before starting the SSO setup process.
Session conflicts happen when an existing Fireflies session interferes with SSO configuration.
2. Why am I getting an “Invalid ACS URL” error?
Verify that you replaced temporary ACS URL https://app.fireflies.ai/sampletest with the actual Post-back URL from Fireflies. The URL must start with https:// and match exactly.
3. Why am I seeing an “Entity ID mismatch” error?
The Entity ID must be exactly fireflies.ai — no trailing slashes and no https:// prefix. Even a small difference will cause authentication to fail.
4. Why can’t users sign in through SSO?
Ensure the SAML app is turned ON for the relevant users or organizational units in Google Admin Console
💡Key Reminders
The Entity ID must be exactly
fireflies.aifor proper service provider configuration.You must replace the temporary ACS URL with the actual Post-back URL from Fireflies.
Users must be assigned to the app in Google Admin before they can access Fireflies through SSO.
The Login URL from Fireflies (app.fireflies.ai/auth/sso) is what your team will use for secure sign-on.
Both the SSO URL and certificate from Google are essential for successful configuration.
Your SAML SSO configuration between Google Workspace and Fireflies is now complete.